For business users and IT Departments, having a secure laptop is essential. Here, we’ve compiled a list of the most secure business laptops available in 2024, each equipped with cutting-edge security features to safeguard your digital life.
Data Backup
Providing Computer Support to Delmarva’s Most Successful Organizations for 40 Years
When experience matters, choose Inacom
Your data network is the central nervous system of your organization. Without a strong, reliable network in place, your staff will be subject to service outages, dropped network connections, annoying distractions, and you may even suffer from the loss of important business data. Proper design, implementation, and maintenance of your computer network will fix problems and create competitive advantages over your industry peers.
Managed Services
Have us take on all or part of your IT management in exchange for a fixed monthly fee. Managed Service clients gain access to our Remote Help Desk, Monitoring and Maintenance services, Managed Backup solutions, and more.
Whether we become your IT Department or we augment your staff, Inacom’s Managed Service offerings will help keep your employees productive.

Computer Repair Services
When your business PC is in need of attention, we can help. Inacom offers on-site or in-house PC computer repair, installations, upgrades for all makes and models. We also sell and provide warranty repair services for HP’s business class PCs

Network Support
Inacom has designed and implemented business computer networks for more than 40 years. From the needs assessment to installation of structured building cabling, to installing the routers, switches, and computers, we have the IT expertise to turn your voice and data networks into a competitive advantage.

Information Technology Consulting
Do you have a vision about how technology can help to grow your business, but you’re unsure where to start and how to implement this vision? Inacom has more than 35 years of experience providing Information Technology support across all vertical industries on the Delmarva Peninsula. Our expertise and best practices are available to help you improve your organization.

IT Security Consulting
Proper access control to resources on your computer network is imperative. Inacom provides IT Security consulting to Delmarva businesses that operate in heavily regulated industries like banking and financial service. We’ve also participated in numerous legal matters, uncovering and analyzing forensic evidence of employee data theft.
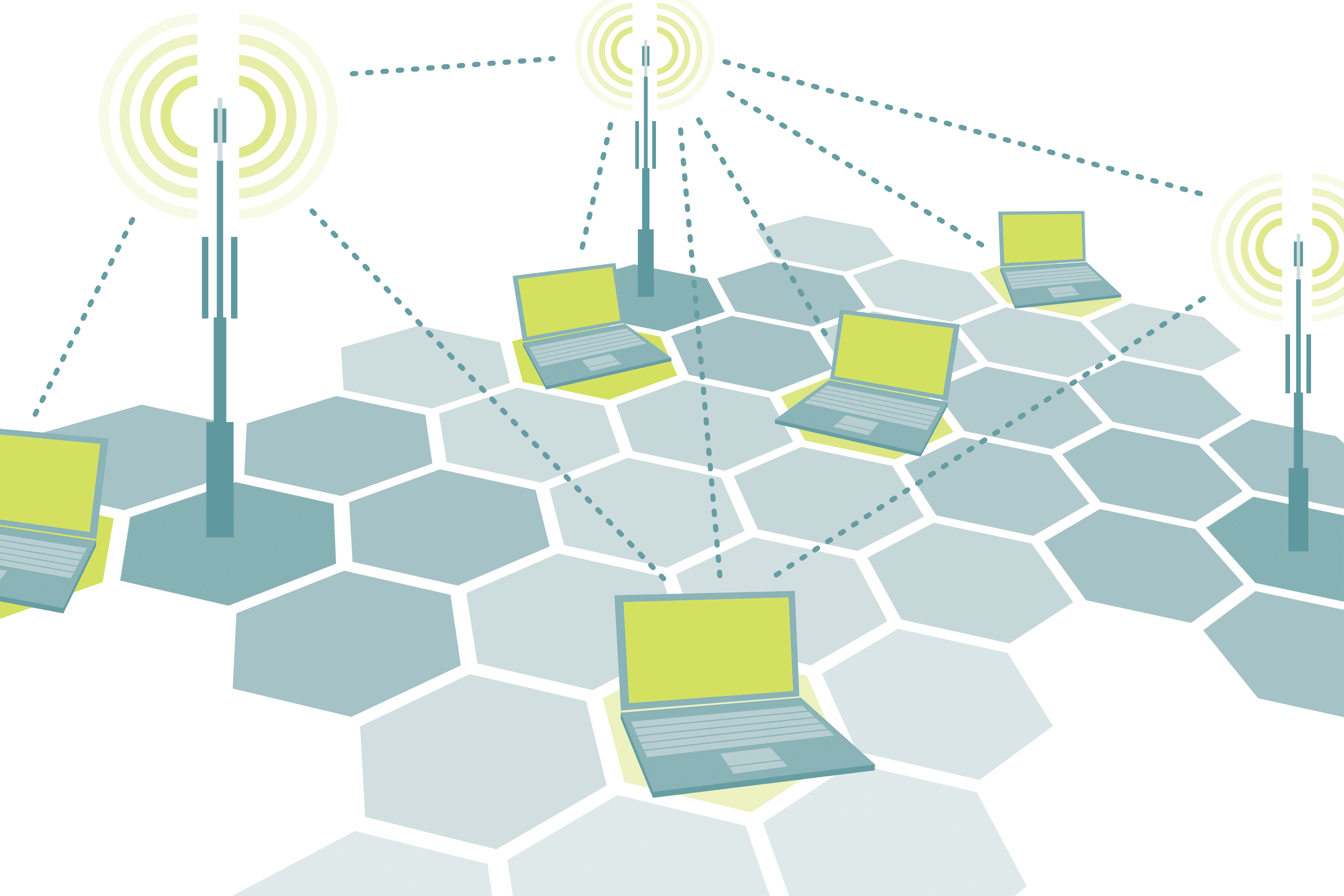
Wireless Computer Networks
A unified wireless network can free your employees from the limitations of cables, overcome the limitations of a physical building, link multiple buildings in a campus or municipality, and introduce value-added networking services to your guests. The wireless networking engineers can help your organization move ahead by creating a strong, reliable, and secure wireless networking topology designed just for you.

Spam and Web Filtering
While the Internet is a great productivity enhancing tool for business, failure to manage Internet content through filtering can kill employee productivity and make your network vulnerable to numerous malware attacks. Our spam and web filtering solutions can keep your inbox clear of distractions, keep employees on task, and generate a high return on your investment.
DarkGate Malware: The New Phishing Threat Lurking in Microsoft Excel Files
A phishing campaign is spreading the DarkGate malware using new techniques to evade security filters, according to researchers at Cisco Talos.
Prescribing Laptops Over Tablets for Healthcare Workers
Healthcare workers are real-life superheroes. Their busy days are filled with managing patients, completing critical paperwork and assisting with emergency medical situations. Having updated, modern technology that is reliable and fulfills these frontline workers’ needs is crucial for productivity, efficiency and communication with their team and patients. Tri-Cities Skin and Cancer, a Tennessee-based dermatology center with a full surgical facility and cosmetic laser center, had been working with Sharp over the past few years for its office equipment needs. It turned to Sharp for a strategic technology switch from a popular brand of tablets to Dynabook laptops throughout its practice to support doctors, nurses and staff.
The Hard Evidence That Security Awareness Training Really Works
Security awareness training works to significantly reduce cybersecurity risk. We have the data to prove it.
Harnessing the Power of Generative AI at Work
By automating time-consuming tasks and delivering insightful data analysis, AI has become an invaluable asset for modern businesses.
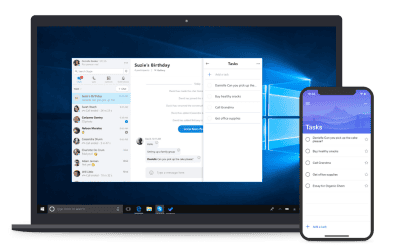
Microsoft To Do: Getting Started and Getting Things Done
Staying organized and on top of tasks is crucial for productivity and success. Microsoft To Do can help.
A Brief Guide to Backing Up Microsoft 365 Data
Microsoft 365 has become the go-to platform for small businesses. However, storing and managing critical data is a challenge many organizations have not considered.
Microsoft and LinkedIn release the 2024 Work Trend Index on the State of AI at Work
Last year, generative AI made its debut and for the first time since the smartphone, people started to change the way they interact with technology. Now, employees are bringing AI to work at an unexpected scale, and the question is, how is it going?
How to Keep your Laptop Secure
Laptops have become an essential part of our lives. They store our personal and professional data, which can be devastating to lose. Therefore, protecting your laptop is crucial. This guide will provide you with a comprehensive approach to securing your laptop.
Microsoft’s Copilot for Security is a Game Changer
As organizations strive to protect their sensitive data and maintain a robust security posture, the need for innovative solutions has become paramount. Enter Microsoft Copilot for Security, a groundbreaking tool that is revolutionizing the way incident response is handled.